Earlier than inspecting how these operations work, you will need to get the terminology proper, and one thing that even skilled nationwide safety reporters, espionage writers, and analysts within the West regularly get flawed. The time period double agent is usually misapplied to explain penetrations of 1 intelligence service by one other. In actuality, these are two very completely different phenomena.
A penetration is an agent who betrays their very own service to spy for a overseas energy. Aldrich Ames, who not too long ago handed away three a long time after he was arrested, was a traitor and a penetration of the CIA by Russian intelligence. He was not a double agent.
A double agent, in contrast, is an intelligence asset who’s knowingly and intentionally directed by one service to interact one other in espionage. The controlling service makes use of that agent to feed data (known as feed materials) —true, false, or combined—to the adversary. They accomplish that to concurrently examine the adversary’s tradecraft, assortment priorities, and decision-making.
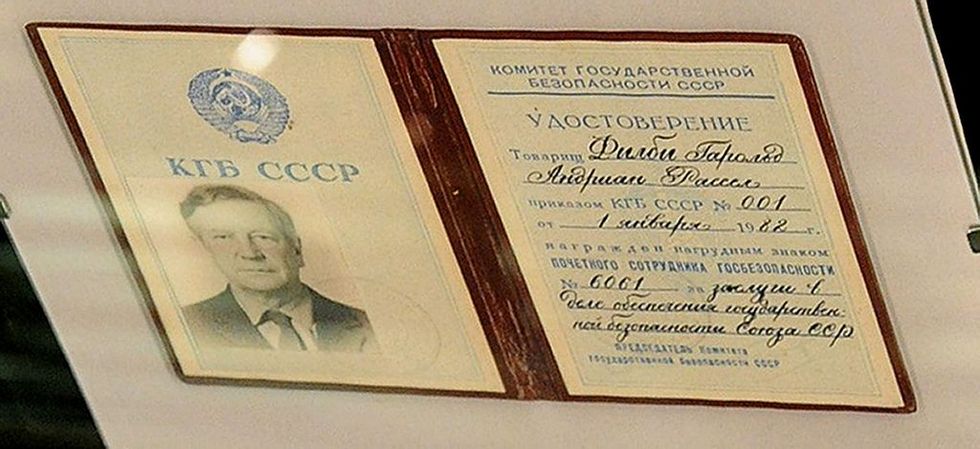
Within the Russian system, double brokers additionally serve a bureaucratic operate: they generate statistics, “success tales,” and operational narratives that show effectiveness to political overseers and in the end to Putin himself. Putin is aware of this; in any case, he was a Lieutenant Colonel within the KGB Second Chief Directorate (answerable for Counterintelligence for the us), and he later headed the FSB himself.
Want a day by day dose of actuality on nationwide and world safety points? Subscribe to The Cipher Temporary’s Nightcap e-newsletter, delivering knowledgeable insights on in the present day’s occasions – proper to your inbox. Join free in the present day.
Double brokers are used within the West and by the U.S. companies, however we don’t misinform our authorities in regards to the origins of the instances or faux they’re actual counterintelligence successes after they attain their conclusion. The excellence is just not educational. It lies on the coronary heart of how Russian intelligence thinks about espionage. Yearly, the FSB publishes an annual report and claims statistics on a whole lot of alleged spies it has caught. The overwhelming majority of them are invented, manufactured, or the FSB’s personal double brokers. In different phrases, they don’t seem to be actual instances.
Russian companies make use of a number of styles of double brokers and operational video games. They’ve many names, together with the initsiativnik, which is a false volunteer who typically “walks in” to an embassy. Additionally used is the podstava, or dangle, by which Russian companies will use the routine of an intelligence officer, diplomat, or journalist and insert the “dangle” proper in entrance of the goal at a gymnasium, reception, or different operate to attraction to the goal. There are nonetheless extra completely different varieties and names for different sorts of double brokers.
These operations aren’t restricted to concentrating on overseas intelligence companies. They’re additionally used in opposition to businesspeople, journalists, diplomats, nongovernmental organizations, and even Russian residents themselves. The target is usually not solely intelligence assortment, but additionally management, because the Russians say, to have the goal “pod kontrolem,” or below 100% operational management and affect. That’s the reason the Russians desire, although not completely, to hold out double agent operations on Russian soil. Overseas, they’re much less assured that the SVR or GRU can absolutely management their double agent throughout conferences with the adversary.
The tip objective is to ensnare, compromise, manipulate, arrest, or extort targets for recruitment and long-term exploitation. A number of examples from historical past assist illustrate Russian intelligence’s fixation on double brokers, courting again to its earliest institutional roots.
The Cheka and later the NKVD/OGPU perfected operational video games within the Nineteen Twenties by way of landmark deceptions corresponding to Operation TRUST. With the TRUST operation, the OGPU (Soviet counterintelligence on the time, one other forerunner of the KGB) created a fictitious anti-Bolshevik underground to lure in Western intelligence companies and Russian émigrés. TRUST despatched intelligence officers to the West, or cooptees, who they intimidated to pose as members of this pretend group that claimed to face in opposition to the Bolsheviks.
The operation ran for years, efficiently feeding disinformation to a number of overseas companies whereas figuring out, neutralizing, or recruiting their brokers. They typically lured Russians house to “assist in operations” solely to have them arrested, interrogated, and normally shot behind the top in a Chekist-style vyshama mera (highest measure) execution. The TRUST culminated within the seize of the well-known British intelligence officer Sidney Reilly, one of the vital celebrated spies of the period, who was executed similarly.
That double-agent custom continued all through the Chilly Struggle, when Soviet intelligence used double brokers not merely to mislead adversaries but additionally to validate its personal competence. Kim Philby, whereas typically remembered within the West as a Soviet penetration of British intelligence, was additionally used as a part of broader operational video games to form Western menace perceptions and shield different Soviet property. Scores of Western intelligence officers or particular operations workforce members had been wrapped up within the Soviet Union or Japanese Europe instantly after World Struggle II, the victims of KGB and OGPU/GRU operational video games Philby had detailed to the us. Most had been finally executed.
In later a long time, the KGB ran managed double brokers in opposition to Western companies to magnify Soviet capabilities, masks vulnerabilities, and manipulate counterintelligence priorities. The Soviet KGB ran a wave of double-agents on the CIA within the late Eighties with false feed materials to elucidate the 1985 U.S. intelligence losses. Rick Ames volunteered and compromised a dozen brokers working for the CIA and FBI (Ames was not arrested until 1994). The KGB and later SVR used these operational video games and false volunteers to guard him, making an attempt to offer CIA and the broader U.S. IC the reason why the compromise could have occurred (Circle of Treason is a basic learn on this era and all the assorted video games the KGB was taking part in to guard Ames with false feeds to CIA and the FBI).
These operations strengthened an inner perception that intelligence success may very well be measured by how convincingly one might affect the enemy’s notion of actuality. In Russian intelligence tradition, the double agent is just not an exception — it’s the ultimate. In in the present day’s FSB, nevertheless, in addition to their overseas counterparts, the SVR, the double agent too typically is used to justify their very personal existence, as a substitute of paying dividends when it comes to tradecraft discovered or secrets and techniques protected. Operations like TRUST are largely a relic of the previous. At the moment, the FSB is simply too busy entrapping harmless foreigners like basketball gamers, academics, and NGO staff.
The U.S. IC and our Western allies have discovered over the a long time that the FSB/SVR and GRU have introduced double-agent instances to their political management as in the event that they had been real brokers caught and arrested, all of the whereas the case was merely that they had been double brokers. They feed statistics from the FSB every year about exaggerated intelligence operations—greater than all of the companies on the planet might perform in opposition to Russia—and in addition declare to have thwarted all of them. These studies attain Putin and the Presidential Administration to justify bigger budgets, which in flip breed extra corruption and line the pockets of senior and center managers.
This isn’t distinctive to Russia; it’s typically the case throughout the previous Soviet nations of Central Asia, the place lots of the companies stay shut and subservient to the Russian FSB and SVR. These companies, typically serving despotic regimes, swear by double agent operations as a result of, in lots of instances and over a few years, the one “spies” they’ll actually uncover are these they falsely created below a double agent operation. They use them in opposition to a spread of unwitting overseas residents, together with in respectable enterprise practices, to extort them and their corporations for cash when introduced up on false expenses.
The follow has been expanded in recent times by the Russian FSB, significantly its counterintelligence division, DKRO (the Division of Counterintelligence Operations), which makes use of double brokers in opposition to journalists, businesspeople, and others to lure them and maintain them hostage for exchanges with the West. DKRO was answerable for the false arrest and imprisonment of Wall Road Journal reporter Evan Gershkovich earlier than his 2024 swap with the West.
In sum, operational video games and the double brokers related to them permit Russian intelligence to form narratives, manufacture threats, and create the looks of omnipresence. They’re soiled methods elevated to doctrine. They usually stay one among Moscow’s only instruments for compensating for broader institutional weaknesses.
All statements of truth, opinion, or evaluation expressed are these of the writer and don’t mirror the official positions or views of the US Authorities. Nothing within the contents needs to be construed as asserting or implying US Authorities authentication of knowledge or endorsement of the writer’s views.
The Cipher Temporary is dedicated to publishing a spread of views on nationwide safety points submitted by deeply skilled nationwide safety professionals. Opinions expressed are these of the writer and don’t signify the views or opinions of The Cipher Temporary.
Have a perspective to share based mostly in your expertise within the nationwide safety discipline? Ship it to [email protected] for publication consideration.
Learn extra expert-driven nationwide safety insights, perspective and evaluation in The Cipher Temporary as a result of Nationwide Safety is Everybody’s Enterprise.